Make your system more secure and start hacking on your smartphone by learning about the best Termux hacking tools available to install on your Android device along with methods. With this check your system for exposure to a specific attack or vulnerability by performing a variety of offensive and defensive scans.
Follow through to know about the best tools with which you can check the security of web servers, and also help with ethical hacking and penetration testing. Today these are seemed to be the best suggested and favorite android applications for security thefts. If you are not a security theft but know how to use these tools even then you can perform this along with penetration testing.
Many tools are available for this emulator all over the internet and you might get confused in selecting out which is best to use. So, no worries just follow through to know.
Contents
Best 14 Hacking Tools for Termux (Camera, Brute-Force, WiFi, SSH)
Nmap – Scan any network
This is also known as the “Network Mapper” which is a port scanning tool. It is a free tool that is the most popular one for efficient network discovery and security monitoring.
It is used for a wide range of services; it uses raw IP packets to know about hosts available on the network, their services with lots of detailed information, Ops, kinds of firewalls, and other information.
Over the years it has won many security awards and has been featured in films like Matrix Reboot, Die Hard 4, and many others. It carries both console support and GUI application.
In this, we can only use the command-line interface of Nmap.
Metasploit Framework – Pen Testing Simplified
This is more than just a Termux tool and is a collection of exploit tools. We would call it an infrastructure that can be used to create our own tools.
It comes in free and it seemed to be the most popular tool in the field of information security. This allows finding vulnerabilities on different paths.
It has the support of more than 2 lakh users and employees to help get the information required and also to identify vulnerabilities in the system.
This toolkit allows simulating real hacker attacks to identify vulnerabilities.
The best thing is that it is supported on all major platforms plus you can also install it on Termux.
Install it in Termix:
Open the tool and type the following command one by one and wait for them to get finished:
pkg update && pkg upgrade –y
pkg install unstable-repo
pkg install metasploit
- Once done it shall be successfully installed, after this type the following command to run it:
msfconsole
SQLMAP – SQL Injection Heaven
This program allows you to check websites for the presence of SQL injection vulnerabilities, XSS vulnerabilities and exploit SQL injection. It supports types of SQL injection and databases.
There are still many sites on the internet which is vulnerable to its vulnerability.
With this, you can check your sites to see that it is vulnerable to SQL injection vulnerability or not.
It is available for all major platforms plus you can install it on Termux.
Also Check: List of Google SQL Injection Dorks for Hacking Sites.
Wireshark – Analyze packets like a pro
This is a popular and well-known professional tool with which you can detect vulnerabilities within a network and among many firewall rules.
It is being used by many security professionals with the purpose to analyze networks, capture sent packets, and scan hundreds of protocols.
It helps to read real-time data from Ethernet, IEEE 802.11, PPP/ HDLC, ATM, USB, Token Ring, Bluetooth, FDDI, Frame Relay and many other sources.
It has command line support and this version is known as TShark.
Nikto – Web App Scanner

This tool is developed in Perl whose aim is to give advice on the web servers which fall into the category of vulnerability scanners.
It was designed with the purpose to find out different kinds of configurations, files, standard or insecure programs on the web servers.
Now keep in mind that it not only shall look for SQL injection problems or improper authorizations but will also open port or active the firewalls. It shall scan the site for interesting files and settings which could be passive to the attack.
How to Install Nikto in Termux:
- Open Termux and type the following commands:
apt update && apt upgrade
pkg install git
pkg install perl
git clone https://github.com/sullo/nikto.git
cd nikto
cd program
- To run a scan with this type the following command
Replace <target website> with the site on which you wish to run the scan
Perl nikto.pI –h securedyou.com
This is all!!
Social Engineering Toolkit – Hacking Humans
This was featured in Mr Robot, TrustedSec’s toolkit is an advanced framework that simulates different kinds of attacks in the social engineering field like phishing attacks, credential collection and many others.
At Elliot, one can observe that they use the ability to replace SMS from it.
The tool is written down in python and is a standard test for protection against unauthorized access in this field with more than 2 million downloads.
Moreover, it is also used to automate attacks and generate hidden emails, malicious web pages and much more.
FSociety Hacking Toolkit – A dream bundle
If you reach this point then you are quite lucky, now we shall get a repository in which all penetration tools appeared on the Mr Robot series.
It carries all its hacking tools which appeared on the Mr Robot series.
Tool-X – Most Popular

This is seemed to be the best one which is designed especially for this. With this, you can install 371+ hacking tools with a single click.
It is developed by Rajkumar Dusad. Now before the invention of this tool, one needs to install necessary tools one by one by searching on Github or on any other site.
Install this which has a list of all the required theft tools. After installing this on Termux, install your favorite tools easily with a single click.
Installing Tool-X in Termux:
- Open Termux and type the following commands:
pkg update && pkg upgrade -y
pkg install git
git clone https://github.com/Rajkumrdusad/Tool-X.git
cd Tool-X
chmod +x install.aex
sh install. aex
./install.aex
- It is now installed. To run type the following command:
Tool.X
Slowloris – DDoS Attacks from your phone
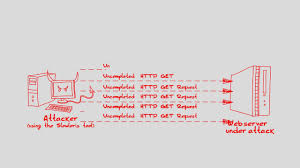
This is a low bandwidth Dos application that is written down in python language. This tool is used to perform an HTTP denial of service attack which slows down or makes the small servers crash.
Use this to perform a Dos attack on the site. It creates HTTP requests and sends headers periodically to keep the connection alive.
Keep in mind that it does not close the connection unless and until the server does so, as it closes down the connection the new connection has been created. The server goes down or does not reply as a result.
Hydra – Brute Forcing Passwords
This is quite a powerful tool that is used to brute force the username and passcode of services like telnet, FTP, ssh and many more.
This is one of the best brute force tools which are used to crack passcodes and usernames.
Installing Hydra:
- It comes in with a simple installation method, for this open Termux and types in the following commands one by one:
pkg update && pkg upgrade –y
pkg install hydra
- It has now been installed successfully.
- To see usage type in the following command:
Hydra –h
- This shall help you guide on how to use it.
IP Tracer – Track IP Address locations
If you are looking for a tool that is able to trace the IP address of the victim then this shall be the best tool to trace it down.
It is coded in PHP and shell; it uses ip-api to track down IP address of the user. It is downloaded by many users.
It is designed especially by Termux therefore you can trace IP of any person by using this tool.
Zphisher
This is seemed to be the best tool for Termux. If you are looking for one which can be used for phishing then give this one a try.
This basically is an advanced version of the phishing tool kit and an upgraded version of shellphish. Inside this, you shall get a tunneling option from 4 tools which are:
- run.
- net
It has more than 30 social media phishing pages and all are in working condition. This feature makes it to be the best tool for this.
Infect
This is a package that allows users to create and send in viruses to any android device, through links viruses can be sent in. Users can also save an infected device from them by clicking on the “save now” option.
Installing Infect:
- For this type in the following command after opening:
pkg update && pkg upgrade -y
pkg install python python2 -y
pkg install git -y
pip install lolcat
git clone https://github.com/noob-hackers/infect
cd infect
bash infect.sh
Seeker
With this, you can find the exact location of the person remotely. It allows hosting a site on a PHP server. It uses serve or Ngrok in order to generate a link that can be forwarded to the target, as the target opens the site it asks for location permission and if the target allows get the exact location of the target along with the direction of Google Maps.
This can be used in Termux as a tool to find the exact location of the user.
Also Try: Download Cain and Abel APK for Android.
FAQs
What is the best hacking tool in Termux?
This question depends on context. However, generally, Nmap and Wireshark are two of the most popular and famous.
Is Termux Legal?
Yes, it is. However, you have to only use it on systems and devices where you have permission to do so on.
How many Hacking tools are there available?
There are well over 300+ well-known packages available out there.
Can I crack a password with Termux?
Yes, you can. This can be done by utilizing a tool such as Hydra or John the Ripper.
Conclusion: Which Termux hacking tool have you chosen?
This was the end of our extensive article about the best hacking tools out there to install in Termux. We have also shown how these can be added and have given a download link with each one of them for ease of use for you. Let us know which one have you picked in the comments below.







Not a termux, but Vooki scanner is also a great tool for vulnerability finding.