In today’s article, we are going to talk about DarkComet RAT Download 2022 which is RAT (Remote Access Trojan) malware program which has been developed by Jean-Pierre Lesueur also known as (DarkCoderSc). Jean-Pierre Lesueur is a security coder of computers and a self-reliant programmer from France. DarkComet is used to control the Graphical User Interface (GUI) of a Computer System.

Contents
About DarkComet-RAT Download
DarkComet is also a part of the RAT Malware Software which grants a user to control the Graphical User Interface (GUI) of any other person’s Computer System. This particular software has many features which a user can use like an Administrative remote helping tool. The DarkComet can also be used for performing malicious or malware tasks to harm one’s Computer System. The primary use of DarkComet is to spy or keep an eye on your targets by Password Stealing, Screen Captures, and Key-Logging.
Read more: AndroRAT APK Free Download – Android Hacking App
A Brief History of RAT (Remote Administration Tools)
The first RAT malware software was developed in the year of 2008 and it started to increase quickly at the starting year of 2012. This program was partly banned and discontinued because of its usage in the civil war of Syria. The purpose of using it in the war was to monitor activists and also the creators or users of it to protect them from getting arrested for different reasons. And now in August 2018 the development of this program has been banned and stopped, plus the download files of this malware software are no longer available over its official website.
More: Cain and Abel Free Download for Windows 10, 11, 7 (2022).
History of DarkComet in the Past Few Years
In the past few years, DarkComet has been used for many malicious purposes which disturbed the environment of some modern countries. These purposes were as follows:
- Booby-trapped Skype Message:
In the past few years, a “Booby-trapped Skype message” was sent to different Skype users. It consisted of a file with a Facebook icon, but actually, it was bait for Skype users. This file was designed to install DarkComet into the victim’s Computer System. Once the targeted victim has installed the file then the Victim’s machine will send the same message to the other people from the victim’s contacts.
- #JeSuisCharlie:
In 7th January 2015 attack was made on a magazine of Paris named Charlie Hebdo. Hackers used the Slogan “#JeSuisCharlie” to trick and trap people into downloading the DarkComet. It was embedded in the form of a picture of a newborn baby and on the wristband of the baby it was written “Je Suis Charlie.” Once the victims downloaded the picture, they were endangered by the DarkComet. The hackers took great advantage of this calamity and took control of many systems as possible.
- Targeting the Government, Military, and Gamers:
In 2012 a Network company named Arbos found proof about the usage of DarkComet to aim the military and gamers by the anonymous hackers of Africa. They mostly targeted the United States of America.
Also download: Commando-VM – Windows Hacking Distribution.
DarkComet RAT Features
Architecture (Working):
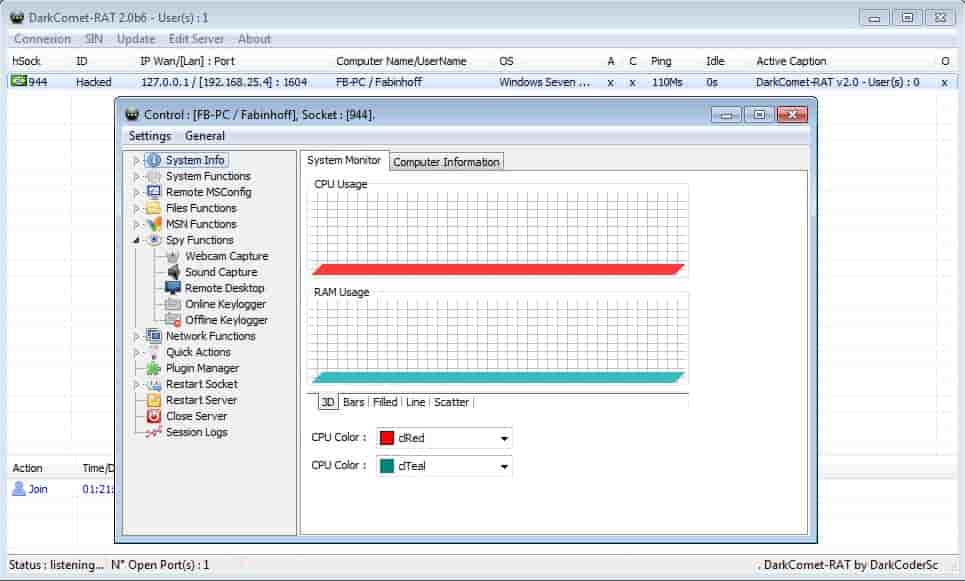
Like many other RAT malicious software, the DarkComet also uses the reverse-socket architecture. The computer systems with GUI enabled and not infected by DarkComet are called clients. While the uninfected systems which are without the GUI are called Servers.
The process of DarkComet execution is pretty simple. The first thing which DarkComet does is that it connects the server with the client and it grants permission to the client to monitor and control the server. At this stage, any of the features which contain the GUI can be used by the Client. Plus there is a socket on the server-side which is opened and then that devices wait for the packets to be received from the controller and then it executes the received commands.
There is a whole list of dangerous features that make DarkComet a critical tool. Some of these features can take complete control of a computer system by granting full access to the client via UAC.
The features of DarkComet-RAT are enlisted below:
- Network Functions:
- Server Stocks5
- Net-Gateway
- Active Ports
- URL Download
- Network Shares
- IP Scanner
- Browse Page
- Wi-Fi Access Points:
- Redirect IP/Port
- LAN Computers
- Server Actions
- Restart Server
- Uninstall Server
- Remote Edit Server
- Upload & Execute
- Close Server
- Lock Computer
- Spy Functions
- KeyLogger
- Sound Capture
- Webcam Capture
- Remote Desktop
- Update Server
- From File
- From URL
- Computer Power
- Shutdown
- Logoff
- Poweroff
- Restart
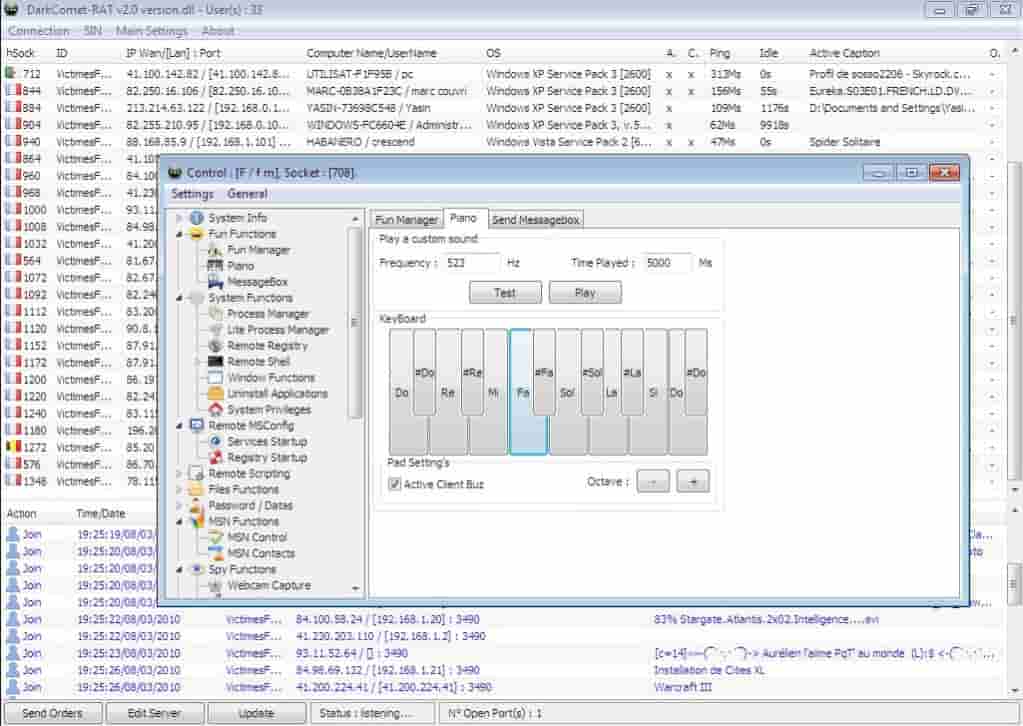
There are also some of the fun features available in the DarkComet:
Fun Features:
- Remote Chat
- Message Box
- Fun Manager
- Piano
- Microsoft Reader
Can Antiviruses detect DarkComet?
As we have discussed before that the DarkComet can also be used for malicious and malware purposes. To keep yourself protected from the attacks of this malicious program, you can install the antivirus software. There are DarkComet removers available over the internet which can detect any malware and delete it completely. Programs like Bitdefender, Norton, and Avast are constantly updated. This increases the risk of detection.
The DarkComet’s infected files generate the following infected files to harm your computer:
- DarkComet
- BDS/DarkKomet.GS
- Trojan[Backdoor]/Win32.DarkKomet.xyk
- Win32.DarkKomet!O
Whenever any of these files infect your computer system the first thing they do is to create a connection to the controller’s computer via socket. Once the connection has completed your computer is ready to take commands from the attacking computer, when the attacking computer sends commands then your computer system receives it and executes the function which is sent by the attacker.
Read: OphCrack Download Free for Windows 7, 8 and 10.
More Hacking Tools:
- L0phtCrack Free Download – Password Auditing Tool
- fgdump (pwdump 7) Free Download
- OpenVAS Free Download
- Metasploit Pro Framework
Update: DarkComet RAT was updated for 2021 to the latest version and tested to work.
A question, “Is it safe to use?” was being asked a lot. The answer is that it is 100% safe to use however, you should only use it on systems where you have permission to do so on.
DarkComet RAT Free for Windows 7, 8, 10 2021/2022 [Updated]
In this guide, we talked about RAT malware software named DarkComet-RAT Free Download which is used for controlling a computer system and it can also be used for the administrative remote help tool. But mostly it is used by hackers for performing malicious activities.
In this article, we further discussed the History of RAT and then we discussed the History and Malicious usage of DarkComet in the past few years. After that, we saw a whole list of features that are included within the Dark Comet. Last but not the least I shared a link from where you can download the latest version of DarkComet RAT which is SAFE!
Note: Please use this tool on systems you have authorized access on. For more information visit their official wiki page.
Version: 5.3.1







Omg, thank you for sharing the darkcomet legacy source code dude. Much appreciated.
Your welcome.
It’s easier to get it from here than Github.
Comments are closed.