
This is a powerful remote administration tool which is a client-server app. It allows users to control other computers with a computer remotely. Plasma RAT free download provides users with the power to establish a connection as well as control over other systems.
This is not only a standard tool instead is designed with the purpose to control a vast amount of computers at the same time. Moreover, it allows to mine cryptocurrencies like:
- Dogecoin
- Litecoin
Contents
Plasma RAT Features
- Edit Hosts File
- Edit startup programs entries.
- Install hooks on local processes like web browsers, IM clients and email managers.
- View current network connections.
- DDoS Attack
- Local windows account and web browsers password recovery
- Website Stress Testing
- Task Manager
- Chat between Client/Server
- Script Execution
- Cryptocurrency Miner
- File Explorer
- Remote Desktop
- Remote Web Cam
- Keylogger
Plasma is a malware recognized by most AV companies such as Avast or BitDefender. This was introduced in 2013. It received most of its updates until 2016 when the project entered a dormant stage of development. It is classified as a mid-tier remote access Trojan due to its unique features that are rivaled by tools like OzoneRAT.
Threat actors continue to use this due to its:
- Stable performance.
- Support for advanced features.
Plasma File Details
%ALLUSERSPROFILE%\windows command processer\cmd.exe\cmd.exe
MD5 checksums:
- 39a31c5ebcaf67118a443cf239fbeb2cexe:
- 13604e19ebbd95974841a789d60f9859
Regexp File Mask
Regexp file mask:
%WINDIR%\SysWOW64\Application Services\appsvc.exe
%WINDIR%\SysWOW64\Diagnostics Troubleshooting Wizard\msdt.exe
Directories can be found in:
%ALLUSERSPROFILE%\PromSchedules
%WINDIR%\SysWOW64\PlasmaRAT
What Environments and OS does it target?
Plasma RAT can target windows machines by surpassing any security measures and built-in security enhancements in windows. Dubbed Moker, it can:
- Take screenshots.
- Record web traffic.
- Monitor keystrokes.
- Export files.
- Inject malicious code into various system processes according to security company enSilo.
Moker can create a user account with administrative tools, open Remote Desktop Protocol (RDP) and gain control over the device of the victim. With this users can:
- Get system privileges.
- Access settings by passing as a legitimate OS process.
Control malware through VPN remotely by using a legit set of user credentials or control panel without any need for a command and control server or internet connection.
SEE ALSO: What is njRAT and How to Download it for free.
How to Use Plasma RAT
Now that you know most about it! It’s time you learn how to use Plasma.
A question may arise that how does malware bypass windows security? A few loopholes and design flaws are there in the windows controls, not vulnerabilities.
UAC, known as the User Account Control, is a security feature. It pops up a dialogue box and prompts users when elevated privileges are requested by a program, requiring administrative rights. So it gained them without the consent of the user by getting onto other programs; there was the exception to UAC security control.
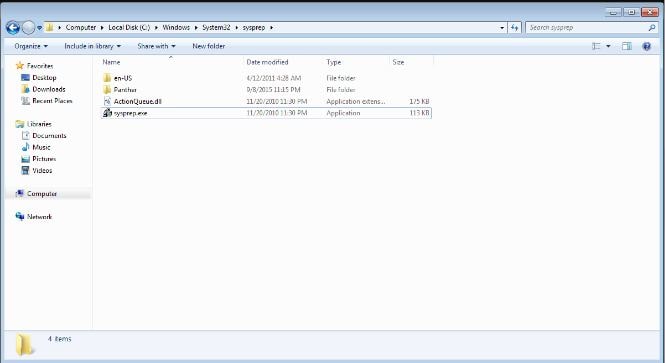
One example is the Microsoft System Preparation Tool, Sysprep, which allows granted permission without any user prompts. Moreover, it also allows the user to install windows OS with minimal intervention by technicians or admins used during large-scale rollouts when it would take much time as well as resources to have someone install an OS on each desktop manually.
Windows enable loading the unauthorized dynamic link libraries DLLs by the authorized apps, design flaw is found in the ways windows pack the DLLs that too on request. Some of the DDLs are loaded there from the system directory in spite of any other duplicate DLLs found in its path.
ActionQueue.dll is the only DLL that does not follow this restriction. To bypass the Windows security, Moker writes the name of the file ActionQueue.dll in the Sysprep directory; they run it so that DLL can run elevated privileges.
CLI-Oriented RAT Tools
- PsExec is a convenient tool for the windows system as it allows users to execute processes on a remote system, provided server service is available TCP ports 445 for 139 and that you have local administrator credentials on the remote system.
- It is first copies executables, exe, contained in the psexec.exe binary, using SMB, under %systemroot%\System32\, installs the service and then starts it. Keep in mind that this step would require credentials. If you are logged with local credentials that correspond with local credentials with a domain account or with one with a username and password identical to a local account on the remote system, the additional credentials are not required.
- Remd is a Windows NT 4.0 resource kit tool that is composed of windows service and command-line clients that provide support to remote process execution. This service opens up a named pipe, \pipe\remdsvc. Its client is used to establish an SMB session to the IPC$ share, authenticated with an account that must have SeInteractiveLogonRight Logon right “Allow log on Locally”.
SEE ALSO: Download Remcos RAT Full Version.
Web-based RAT Tool
One of the big issues in confronting information systems IS managers is how to provide secured access to corporate IS resources to all people who are located outside the corporate network physically.
In today’s connected world and society, traveling, salespeople, telecommuters and working staff extra hours all require some real-time access towards resources on corporate networks. Now, for security concerns, resources like databases, sales tools and emails are protected by firewalls so that users outside the organization cannot access it.
Today different companies are finding ways to provide cost-effective network access to all their remote as well as mobile employees. Most remote-control solutions are one way to provide such access. Web-based small administrative tools such as GotoMyPC is a hosted service that provides and enables secured browser-based access to any internet-connected Microsoft Windows-based system. It carries the following features:
- Screen-sharing viewer.
- Grad and drop file transfer.
- Remote printing.
- Guest invites and chats.
The corporate administrators have all the access to extensive management and reporting tools that are used to enable central control over the remote-access services. As you choose for a device, the following characteristics have to be considered the TCP ports required to use the remote administration feature:
- The supported authentication mechanisms
- System authentication implemented by Windows
- Application-level authentication only.
Plasma Alternatives
Disclaimer: Please only use this tool in a controlled lab environment for educational and informational purposes only, with permission. We will not be held responsible for any damages you cause by using it.
Download Plasma RAT For Free (2022 UPDATED)
Here is the most famous Plasma RAT download you have all asked for, a remote administration tool that has been built on with the focus of hacking crypto coins such as Bitcoin and others.
As requested, this is the full version and has not been modified in any way by us before uploading.
Build: v1.5.06 (Latest Version)






