
SQL Dumper allows users to dump or export selected SQL server database tables into SQL insert tables. It is regarded to be the best in its category! These are saved as local .sql which carries all the data that is required to:
- Create a duplicate table.
- For backup purposes.
The user has the choice to create an individual file for every table or combine all selected tables into a single file. SQL Dumper download 2022 comes in the latest version!
This is seemed to be an excellent tool for all the programmers and make each process more efficient and effective. Though it is a bit expensive it saves a lot of money in the long term as it frees up labor hours and also allows making the best decisions.
SQL Dumper Features
- It comes in free.
- Safe to download.
- It works with all the versions of windows.
- User can choose where they want sqldumper.exe utility to transfer the file, this needs to be created before the transfer and it allows for easier organization.
- It is able to move a large amount of information. Make sure that your hard drive has adequate space before beginning utilization else the process fails. If space is enough then the software can make the export of data much faster and easier.
- It carries special features which allow users to good control and flexibility. Such as with a foreign key feature you can set certain order to tables in a text file like this the future information can be inserted while avoiding collisions and errors.
- Another good feature is the primary key identity which guarantees identity field value.
This is an advanced, excellent yet automatic tool that is used to test links that may carry SQL injection problems in windows.
- It provides support to multiple online search engines.
- Automated analyzing and exploiting from URL list-automated search for data in the big list.
- It is an automated analyzer for injection points by using URL, POST, UserLogin or UserPassword.
- Dumper is able to support dumping data with multi-threading.
- The exploiter supports up to 100x threats.
- Both analyzer and dumper support up to 50x threats.
- Comes with advanced WAF bypass methods.
- Carries an advanced custom query box.
- Dumper is able to dump a huge amount of data with great control of delay each request (multi-threading).
- Admin login finder.
- Hash online cracker.
- Trash system.
SEE ALSO: Download DroidSQLi DB Hacker App for Android.
How to Use SQL Dumper for Hacking a Database
Although the version changes slightly, the principles are the same so if you are using 8.3, 8.5 or any other then it should not matter.
This involves the use of proxies and dorks. If you do not know how to create these then:
- Start by preparing the dork list. There are tools that help you do this or it can be Googled as well. There are some paid services like Ezdork and many others. All this is up to you; you can also create a proxy list.
The first thing you want to do is add proxies, click the proxies list that you would see on the toolbar at the top button known as Apprend.
Be sure that you have chosen proxies copied to your clipboard and select https:/socks4/socks5 depending on which you are copying into the dumper.
- Once the dork list is there open it. Following is how 9.7 looks
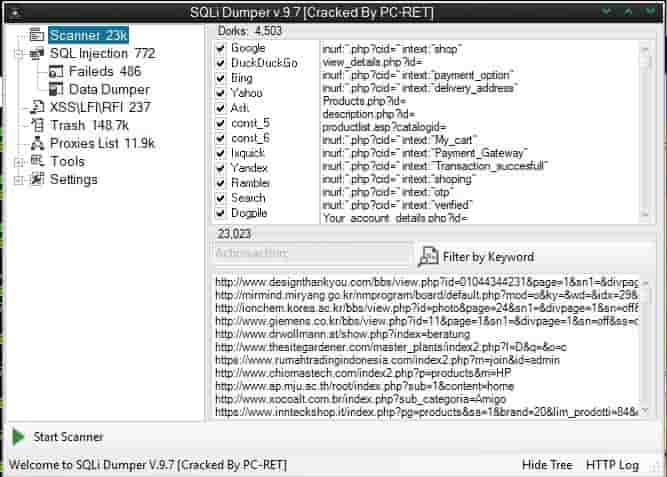
In the picture, inurl is where you copy and paste chose dorks. If you are using this for the first time then the second part of it where you see https:// shall be blank. Don’t worry this is normal.
- Now you are ready to scan. Click on start scanner there in the bottom left of the program.
Depending on how many dorks you have selected to use and how many threats you have set along with internet speed and overall power of your system or RDP this might take some time. Leave it for some hours to a couple of days.
- You would see the scanner option has started to go up in number as ours in the image below shows 23 links.
- Chose SQL injection tab on the left side, set threats and click start exploiter.
- You shall now see websites filling up in it or in the exploitable section of the software.
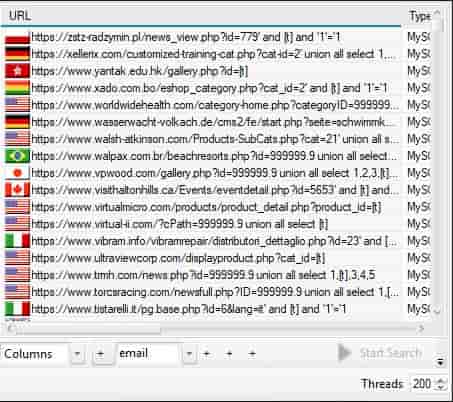
Speed depends on internet connection and over system performance. Once finished the run and check all websites from scanner list. You can double click on any or click right and then select Go Dumper.
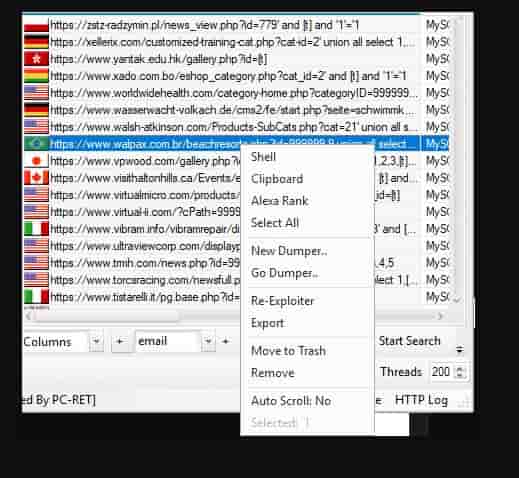
- You shall now be taken to the dumper module.
In this list, you shall see the database name for MYSQL and the site you are exploiting is using. Click on it and then chose to get the columns button.
SEE ALSO: Download Havij Latest Version – Recently Updated.
This shall start to pull through tables within a certain database. You would be looking for something along the line of “users” “customers” “members” “logins”. Some/a lot of websites/stores, etc will use prefixes too like “pvt_users” “forum_members”
- Once tables have been generated for the selected site then you shall be presented with:
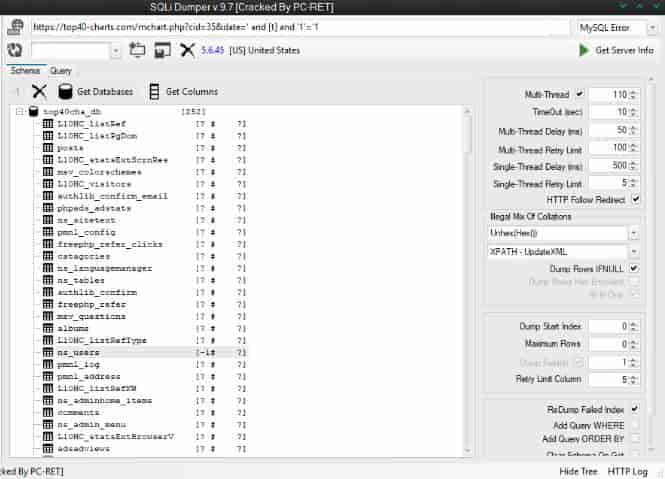
We have highlighted ns_users table; a place where email and password columns shall be stored and if looking to make combo list then that is what we want.
Highlight selected table and hit get columns.
Some sites might store emails separately to where passwords are stored. User:Pass lists are very useful. The one we chose while writing this article it’s a User:Pass kind of site
Select data that you wish to dump and hit the dump data button.
SEE ALSO: Download SQLNinja SQL Injecting Tool for Windows.
This shall change the data dumper screen when it starts gathering data from columns. You would end up with:
Sites carry various tables, search the one that stores userbase information. This stable we have stumbled across is for some type of login either with their CMS, shopping or forum/blog.
If you wish to exploit the admin panel then you can gain access to the website and root server and then use it for your own personal reasons along with being able to strip data of each site hosted on a specific server.
SEE ALSO: How to Secure Your MySQL Database Server and Data.
SQL Dumper Download 2021/2022 – The Best DB Hacking Tool
I hope you enjoy using SQL Dumper download, this is one of a kind tool for hacking and playing around with SQL databases.
Version(s): 8.1, 8.2, 8.3, 8.5 10.1, 10.2






