
W3AF is abbreviated as web application attack and audit framework. It is an open-source web application security scanner. The tool acts as a vulnerability scanner and an exploitation tool for web applications. W3AF Free Download is used to provide information regarding security vulnerabilities that are used in penetration testing engagements. The scanner comes with a GUI (graphical user interface) and a command-line interface.
The scanner has two main parts:
- The core
- The plug-in
The function of the heart is to coordinate the entire process and also provide features that are used by the plug-ins that find the vulnerability and exploit them. By using a knowledge base, the plug-ins are connected and share information.
Contents
What is W3AF, and do you need it?
The goal of the W3AF project is a framework that is used to find and exploit the web application vulnerabilities that are easy to use and extend.
The most questionable and challenging part, while securing a web application is how to identify the vulnerable parameters and then define the real risk that lies. The following video shows how to identify and exploit SQL injection vulnerabilities easily. Moreover, the video shows how to extract information using web application web loads.
Through plug-ins, the vulnerabilities can be identified. The weaknesses are sweet and short pieces of Python code that are used to send a specially crafted HTTP request to the forms and query string parameter to identify misconfigurations and errors if any.
The tool is convenient and easy to use for novice users. It is fully customized for developers and hackers. It is built to provide ease to the users.
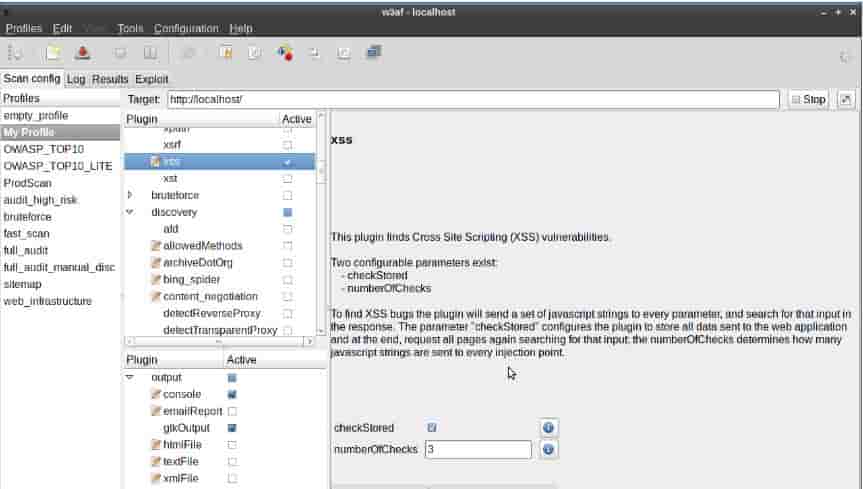
The GUI (graphic user interface) of W3AF along with its automated scanning features comes with expert tools that allow advanced users to craft manually and then send customized HTTP requests, generate requests in an automated manner and also cluster the HTTP responses and much more.
Once you understand the basic concepts behind W3AF, it becomes straightforward to use. The features shall introduce you to the overall idea and notion, and you will get to know everything before running a scan.
SEE ALSO: Acunetix Web Vulnerability Scanner Tool.
W3AF – Web Application Scanning Tool
The black box web application scanning process, however, is straightforward and easy. It has the following details:
- You need to identify all the links, forms, and the query string parameters
- Then you are required to send the specially crafted strings towards each input and then analyze the output
- Then you need to create a report along with all the findings
If you do not have the right tools, then yes, this process is complicated and could not be performed in the right way. So, you need to have the right tools.
How W3AF Works
The W3AF follows the steps that you, as a user, shall perform in a web application penetration test. To do this, you need first to define the different types of plug-ins that are going to be called by the core in a specified order.
It all starts with a targeted URL that is provided by the user. The URL, forms, and query string parameters are first identified by W3AF, in the application using crawling plug-ins. The web spider is an excellent example of this type of plug-in. The web spider is used to extract URL’s from the specific page, follow those links and again extract URLs from it. This process would create a full link of the application and also form its map.
As the application gets mapped, the audit plug-ins shall send the specially crafted strings towards each parameter to trigger bugs in the application’s code. The bug shall be reported to the user once found. SQL is the most frequently used audit plug-in that shall find error-based SQL injections.
Then the identified vulnerabilities, errors, and debug messages all are reported to the user with the help of output plug-ins. These plug-ins are used to write the words in different formats that suit your needs. In most cases, a simple text file is what the user needs but to integrate into other tools XML format is there too.
SEE ALSO: Nmap Network Security Scanner Tool.
What you can configure in W3AF:
Plug-in Configuration
The plug-ins may have configuration parameters in all most all the cases where the plug-in has default settings set. You are recommended to read the setting help and in some case the plug-in source code so that you understand quickly and precisely what will happen if you change the configuration.
Global Configuration
The settings of framework wide change the core behavior and are then split into two:
- settings
- HTTP settings
As with the plug-in configuration the settings in global configuration come at a default value and therefore must be changed with care. When you change the environment here, it may reduce the performance of the scanner and have the framework to generate thousands of unnecessary HTTP requests and much more.
Allows you to save your settings
The user-defined settings can be saved using the profiles. Saving settings helps the user to run their scans many times and in some particular cases, run them with slightly different configurations. It now becomes an easy task to create, save, and load profiles that did from within the user interface.
SEE ALSO: Burp Suite Professional Vulnerability Scanner.
Where to get W3AF from
If can download the following source from Git Hub repository if you are a Linux, BSD or Mac user:
Git clone https://github.com/andredriancho/w3af.git
- Cd w3af
- . /w3af-GUI
Once you run this command, you shall get a list of unseen powers and dependencies to run to install them. The best thing for you is that you will be having W3AF run in a few minutes and only by running the commands that are returned by w3af_gui.
The framework has two different dependencies; one is for the console, and the other is for the graphic user interface. If you do not want to use the GUI, you can run w3af_consile and install those dependencies.
Alternatives
- Wapiti Web App Scanner
- Nikto – Web Server Scanning Tool
- OpenVAS – Vulnerability Scanning Tool
- Nessus Pro
Download W3AF – Free Web Application Scanner Tool
We have highlighted for you regarding W3AF download is a web application attack and audit framework. I hope you will at some W3AF tutorials and learn how to use it effectively. It is a great tool that is open-source. Leave some comments below and tell us about your favorite device.






