If you are looking for guides and tutorials to learn how to DDoS someone like a professional ethical hacker then this is the best DDoS guide of 2022. Before we jump into the detailed stuff on DDoS, let’s assume you just came back from your office.
As soon as you entered your house, you turned on the lights, air conditioner and put a couple of bread slices into that ancient toaster of your ancestors. As soon as you pushed the toaster’s button “boom fuse blows up”. This tutorial teaches you how to DDoS an IP Address, Network or PC.
Now just try to understand what happened there. Your toaster was faulty, as soon as you switch it on, it was flooded with more current or electricity than what it could actually handle. The fuse blew up and it saved the whole system. The same stuff happens in case of DDoS as well. What you need to understand is the information processor. When it is exposed to too much of information or traffic which it can’t handle so it blows up.
Contents
So, What is DDoS and a DDoS Attack?
Now the question is what does DDoS stands for? It is the abbreviation of “distributed denial of service”, and it is a little more complicated than a simple DoS attack. Though both of these attacks serve one purpose that is bringing down a website by flooding its server with a lot of information or traffic.
In the Dos attack usually, one source or a computer is used to send information to the victim’s website. Whereas in DDoS attacks multiple sources of information or computers are used. The number of attackers of computers may vary from 100s to 1000s depending on the strength of the target website.
How to DDoS Someones PC, IP Address or Network (Ethical Hacker Way) – For Beginners
There are many ways of pulling of DDoS attacks. The more the method is effective the more it will be difficult to execute. In order to launch more powerful attacks, the hacker usually hires a dedicated botnet to teach the victim a lesson.
Let’s show you how to DDoS!
DDoS Attacks are Measurable
Some studies and research on the topics suggest that just about 82% of DDoS attacks last less than four hours. About 34% of such attacks have a volume of a hundred MBs to one GBs in terms of their bandwidth. Only 10% of the DDoS attacks have a bandwidth of 10GBs. For the understanding purpose, 1GB/s of DDoS attack is big enough to bring down most of the websites. As we know hosting companies don’t provide much of hosting for small to medium size websites, or people usually don’t bother to get more bandwidth. Note we are not talking about the google or yahoo size giants here.
We are not saying that DDoS attacks are of 10 GB/s at max in terms of bandwidth. One of the biggest attacks was the Mirai bot attack in 2016. That attack’s bandwidth was about 1 terabyte and it took down the Dyn DNS provider. As a result of this attack, some big names like Reddit and Twitter also went down.
Nowadays it’s not difficult to be part of some big bot network, even young kids become part of such big attacks and flood target servers with traffic. Unfortunately, such type of attacks is growing because more powerful tools and computers are becoming accessible easily.
Read: How To Secure your Website from Hackers (Website Security Tips).
Why do Hackers DDoS Someone?
If we compare this type of attack with other types of cyber-attacks, these ones are quite destructive in nature and very difficult to execute at the same time. Such attacks usually don’t have any financial objectives. Theoretically, you can say hackers might use this tool to attack their competitors. Just take the example of a hosting company, a competitor can easily use DDoS to destroy the reputation of a competitor company. If he could bring down its servers. Similarly, small e-commerce stores can bring down their competitor’s websites and take advantage of a sale day like black Friday.
In some cases, the hackers use DDoS as a tool of extortion. They will demand money from the website owner to stop the attack. Sometimes hackers use this attack as a smokescreen or a disguise to infect the website with some sort of malware or to extract some important data. But mostly such attacks are carried by amateur hackers to test their skills so that they could brag about their abilities in front of their social circle. Sometimes hackers just do it for fun.
Botnets: The most effective method
You must be wondering what a botnet is. A botnet is a group of internet-connected machines or computers that are installed with malware. As every device is infected with malware so they obey their admin. The big botnet networks own millions of computers over the internet, which may physically be located anywhere in the world. Usually, owners of such infected computers don’t even know that they are a part of such big network.
Normally such botnets are used for different types of illegal purposes. For example, phishing, collecting user data, or even cryptocurrency. But at times such networks are also rented to other buyers who need to carry out a DDoS attack.
Read: How to Protect your Networks from DDoS Attacks (DDoS Mitigation Guide).
Top Free DDoS Attack Tools of 2022
Small groups of hackers usually don’t have access to such big botnet networks so they just rely on their own computers. Such small-scale hackers use different types of tools to direct traffic to the target server. Well, we understand that one computer can send only a limited amount of traffic to a given server.
But things change dramatically if you crowdsource a few hundred computers. One of the biggest hacktivist groups Anonymous has used a similar approach to launch a similar type of attack. What they do is they ask their followers to download a particular software or malware and target a particular server. Meanwhile, they are connected with others through different messaging services.
Here is a couple of software that are used by hackers to launch DDoS attacks:
- R-U-Dead-Yet.
- LOIC which is an actual short form of “Low Orbit Ion Cannon”
- Tor’s Hammer
- HULK google to learn more about this tool
- DDOSIM this one is another great simulator or DDoS
Please note: You will need to download LOIC DDoS attack tool in order to launch medium to high powerful denial of service pings.
Download LOIC (Low Orbit Ion Cannon) Free Latest Version
How to DDoS an IP Address Using only CMD (Command Prompt)
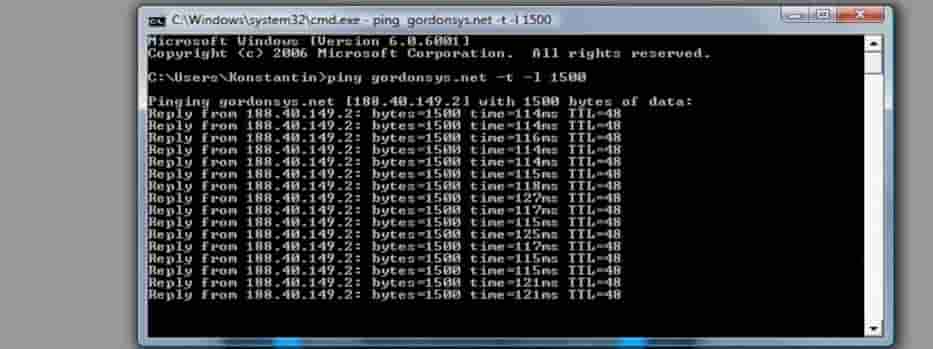
This one is one of the most basic attacks, also known as “ping of death” in this type of attack hackers use cmd in windows to send an abundance of packets to any given IP address.
This type of attack normally works great for comparatively small targets considering the sources available. Hackers usually target:
- Hacker a target one single pc by finding its IP address. In order to carry out the attack on a single computer, the hacker must have to find its IP address so that he could target it with an abundance of packets.
- Other easy targets for such attacks are the Wi-Fi routers. All you need to do is to flood the router with a lot of traffic which will stop it send internet packets to the connected devices. Another way a hacker uses such an attack is to target one single pc to disconnect from a wifi router.
- Though ping of death is very basic in nature and it is effective against only small targets. But if hackers use multiple computers to attack a target they can get the desired results. They can even bring down small websites with limited bandwidth capacity.
Read: Learn How to Hack WiFi Network Passwords in 2022.
Send unlimited requests using Google Spreadsheets
Using spreadsheets of Google, a hacker can bring down a small website. In this type of attack, the attackers use a script that continuously inquires the target website to send a particular file that is stored in its cache. This file can be an image or pdf. He will write the script in such a way that it will keep running in a loop.
Usually, DDoS attacks use a huge amount of information packets to send requests to the target website, but in this type of attack, the attacker instead keeps asking for information from the webserver. In other words, the attacker won’t need a huge amount of computers or a botnet to bring down the website or its service.
Teardrop attacks: Send data one by one
Anyone who understands the basic working of the internet knows that information sent over the internet is usually sent in small pieces instead of one single piece. When some data is transmitted from one end to the other it is divided into multiple pieces and then it is assembled in one piece on the server end.
The server knows to end and to start packets of one big file through parameters called offset. It not only knows their starting and ending points, but it also knows their reassembly order.
Teardrop involves sending a huge amount of senseless and overlapping or non-functional parameters to the server. So the server tries to assemble the data received but it fails to do so, in order to reassemble the uploaded data quickly it uses a huge amount of server resources, and eventually, the website goes down.
How to Amplify a DDoS attack (The Professional Hacker Way)
Hackers at times use DNS reflection, in order to achieve a multiplier effect. This involves a number of steps to pull off:
- The first thing the hacker needs to do is to forge the IP address of the target.
- Once the hackers have taken the identity of the target he will send endless requests to the open DNS.
- Now in response to the requests by the hacker the DNS resolver sends back data or information to the victim server whose identity has just been stolen. Remember the size of the information sent back to the target is bigger than the requests which are sent to the DNS resolver.
So how much every bit of information is amplified? Every one byte of information that is sent by the hacker to the DNS resolver becomes 40 bytes. Now assume if hackers use a botnet and the whole process will end up DNS sending 100 GB of traffic to the target website.
The different types of DDoS attacks:
The DDoS attack can be categorized into 2 main categories:
- Application Layer.
- Network Layer.
Network Layer Attacks: Everything you need to know
In this type of DDoS attack, the website’s infrastructure is targeted by sending a huge amount of info. Though you might have seen adverts claiming to offer unlimited or unmetered bandwidth. But don’t fall for such offers, theoretically, you can say that you won’t have to get worried about the traffic amount or bandwidth.
To understand it more comprehensively let’s take an example of a website that has monthly traffic of about 15k page views per month and 100s of pages. This website would require 50 gigabytes to run. Remember this amount of traffic is expected to be dispersed over the entire 30 days. A website with such resources won’t be able to survive a DDoS attack as even a small-scale DDoS attack can generate that much of traffic within an hour.
In such a case, the hosting service will shut down your website until the traffic becomes normal. Well, you can say that this is pretty cheap on the hosting provider’s side, but this is done to avoid any kind of spillover which might result in affecting other clients. Network layer attack can further be divided into many types some common one is given below:
- SYN Attacks. Synchronize attack is requested which a computer transmits to the webserver to sync the underlying two devices or machines.
- DNS reflecting.
- UDP amplification attacks.
Well, one weakness of this kind of attack is that because of its immense amount of traffic the victim can easily figure out the type of attack is happening on their web server.
Application Layer Attacks: Everything you need to know
This type of attack is more complicated and precise in nature as they tend to target those tools and software which are used by that particular website. Remember such software is sometimes crucial for a website’s functionality. For example, in such an attack, the hackers will target WordPress installation, scripts, and database communication.
Usually, such programs or scripts are not designed to handle such types of attacks or traffic or requests. So in other words, even a small-scale DDoS attack can dismantle these scripts or software.
Usually, an application-layer DDoS attack involves a huge amount of HTTP requests. This exploit is executed using two simple HTTP requests that are Post and GET. These commands are commonly used in web pages to send and retrieve information. The POST request is quite complex uses a lot of resources as compared to GET requests.
It is complex in the sense that the processes started by this command are usually resourced intensive on the server-side. A huge amount of HTTP requests will further generate a big amount of internal server requests which results in a crash of the whole website.
How to protect yourself against a DDoS (DOS) Attack?
Wireshark: Actively Monitor your Networks
It is a great tool to diagnose if you are going through a denial of service attack or not. It offers you some great features, for example, you can see what ip addresses are connected to your server and what amount of packets they are sending.
But don’t forget if the attacker is using VPN then you won’t be able to see the real IP address. And if the attack is coming from a botnet then you will see a big amount of IPs connected with your server. You can google further about the usage of Wireshark.
If you are using windows, it comes with a built-in tool known as Netstat. It along with many other statistics shows you the details of devices connected to your server.
In order to use this tool, just type netstat –an in your windows command prompt and it will provide you with the complete details of your connections. It will show you the internal IP as well as external IPs.
Read: Kali Linux Hacking Tutorials for Beginners: The Definitive Guide (2022 Edition).
Keep an eye on traffic, is it an attack or traffic spike?
Traffic spikes are quite common and on some occasions, they can be immense enough to bring down the websites. If a website is designed to handle a limited number of users at one time let’s say 50 users per occurrence. It is highly likely that the website will crash if 500 user visits it at the same occurrence or time.
A major sign of the website is under attack is slowing down the performance of the server. Service unavailable errors and requests start to take more time, for example, normal requests which are completed within milliseconds start to take longer.
Also read: 8 Best Free Software Firewalls for Windows 10/11 PC (2022).
Let your Internet Service Provider know that you are under attack
Keep your ISP in the loop, usually ISPs and hosting providers have already a planned response for such attacks, but just contact them and keep them in the loop. Be prepared for any of such situations in advance.
Always have an incident response plan or disaster recovery plan ready:
Every website owner should have a response plan just in case the website comes under attack what steps should be taken. Every organization has its own plan, but below are a few steps which should be covered:
- Keep a whitelist of critical IP addresses. For example your internet service provider, traffic sources, your clients and business partners, etc.
- Set up an alarm for traffic spikes.
- Keep monitoring connections and terminate the unnecessary ones.
- Keep your server updated with an extra bit of bandwidth and server-side resources.
READ: How to Protect your PC and Network from a DDoS Attack.
Watch for any virus or malware infections
In many cases, hackers use DDoS attacks as a disguise to get access to sensitive data. When the attack is on don’t panic. Make sure your server is not infected by any kind of malware and your data is saved. Don’t forget to scan your server once you are back live.
Update: We have added LOIC and a guide to prevent from such attacks happening to you.
Another tip: Online stress testing platforms are also a way to test your sites and web apps. These tools have server farms that send massive requests at a time to your provided IP address or URL. They provide you with real-time graphs and other CPU-related information.
Are you safe from DDoS Attacks?
To sum it up, always keep your hosting and web server up to date and always keep a plan to follow in case of a DDoS attack. You should have mitigations in place and should have DDoS protection from your hosting company or provider. This will need you to have a much more powerful server and network connection to overcome the attack. I hope our how to DDoS Attack Someones PC, IP or Network guide was helpful.
Please be aware that this is not a joke and is serious, even if you try ddosing your friend or even someone on discord can get you in trouble, so please be careful how you use our tutorial. You are responsible for your own actions, only use these methods on servers, PCs and systems that you have permission to use and do so on. Let us know any of your DDoS Attack methods in the comments.






Pretty interesting to read
Can you teach about SYN flood?
Hi, thanks for your suggestion, I will also add a topic about this.