
WiFi hacking and cracking WiFi passwords is a very popular topic on the web. Everyone wants a free internet connection, right? Well, today you will learn How to Easily Hack WiFi Password in 2022 using the PMKID attack method for WPA2 and WPA. This is all possible because of a new vulnerability just being discovered by a security researcher called ‘Jens Steube’. This is not an easy task and does require some basic knowledge of how computer networks work. You will be required to enter some commands in the CLI (Command-line interface).
This step-by-step guide about WiFi networking hacking and security testing will require lots of patience and focus. This attack works on all WPA and WPA2 enabled networks that use Pairwise Master Key Identifier or PMKID. The great news is that it works with all modern and new wireless routers from all brands including Netgear, TP-link, Linksys, Asus, and D-Link.
Updated 2019: This Wifi hacking guide has been updated with new methods while working with different weaknesses in the WPA2 and WPA protocol. You can also crack Wifi passwords using Android apps.
Updated for 2022: We have also added the guide for hacking WPA3 Wireless passwords. The video version has also been updated.
Let’s start!
Contents
Common myths and facts about WiFi Hacking
- There is no such thing as WiFi hacking software, all these are malware-infected programs used to infect your computer with malware and viruses!
- Not all wireless networks are easy to hack, and some are also hack-proof.
- Not all attack types and techniques will work on a different network.
- The WPA and WPA2 wireless protocols both have their own security improvements and features.
- The only popular method that works is by using a brute-force attack with a wordlist of common passwords. If you don’t know what a wordlist is, it is a file that contains hundreds of thousands of commonly used passwords, names, and dates.
How to Hack WiFi Password in 2022: New PMKID Attack Method (WPA2 & WPA) – Updated
Before you continue any further please read the disclaimer statement below:
SecuredYou.com will not be responsible for anything that you might do by following our tutorial. This is ONLY for educational purposes and should only be used for improving the security of your own wireless network or which you have permission to do such things on. We will not be held responsible for any rules and regulations that you might break in your country.
If you agree please continue reading this article if you don’t please do not continue further.
Request PMKID from the router
Unlike older techniques where you had to wait until a user connected to the access point so that you can capture the 4-way handshake that is of EAPOL. This new method for finding out the password credentials does not require that anymore. The attack works on the RSN-IE or Robust Security Network Information Element. It only uses one frame which it requests from the wireless router.
Install Hcxdumptool & Hcxpcaptool
This is a tool that will help you to capture the PMKID packet from the access point. After capturing the frame, it can also dump it into a file for you. Below are some features of Hcxdumptool:
- Can easily capture identities and usernames from a WLAN.
- Can easily capture passwords, plain master keys, handshakes and PMKIDs from traffic on WLAN.
After installing this tool run the below command in the CLI.
$ ./hcxdumptool -o test.pcapng -i wlp39s0f3u4u5 –enable_status
The command displayed above will dump the frame to a file.
After doing the above step now you will need to extract some contents from the frame file. This will be in the pcapng format. You can easily convert this into a hash format which the popular program ‘Hashcat‘ can accept. Use the below command to extract the pcapng file.
$ ./hcxpcaptool -z test.16800 test.pcapng
Hashcat is a tool used a lot in the security and penetration testing field. It is used by both hackers and researchers for finding out passwords by cracking their hash. After finding out the hash of the password you can enter the password in hashcat and it will find it out for you. It will take some time depending on how complex the password is of the wireless network. Enter the cmd below and run hashcat.
$ ./hashcat -m 16800 test.16800 -a 3 -w 3 ‘?l?l?l?l?l?lt!’
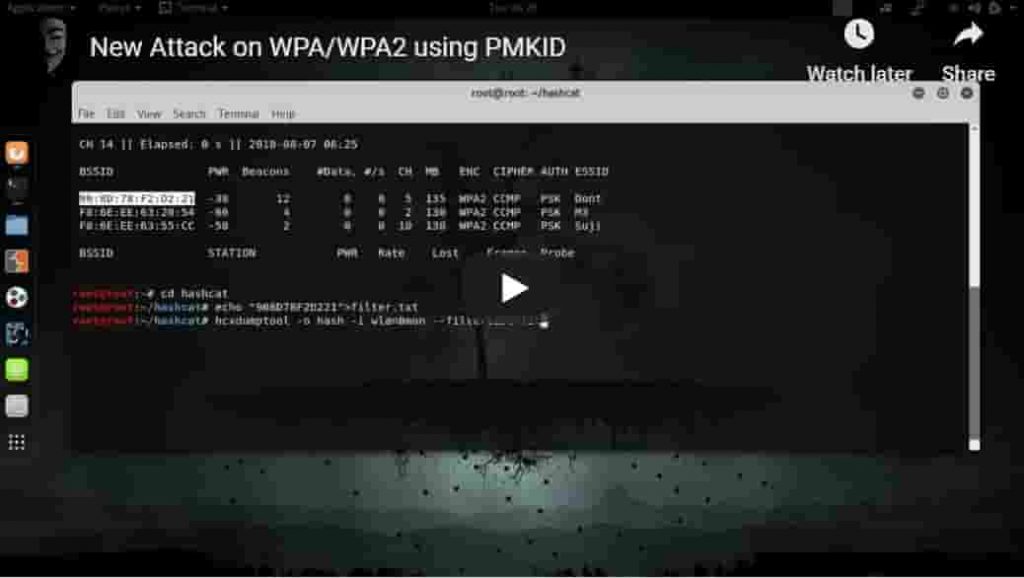
Below is a video-based PMKID attack tutorial
This will make it a lot clear for those who are new to this field.
Modern Wireless Routers are also supported by this new WiFi hacking method
The researcher who discovered this bug in the first place has said that it supports most of the routers out there. It supports all 802.11b/g/n/p/q/r/i that have roaming enabled.
It does not support WPA3, it has a lot of mitigations in place and is a much more secure protocol compared to WPA2. The reason behind is that it uses SAE or Simultaneous Authentication of Equals.
How to Protect against PMKID Wifi Hack and Secure your router?
Well, the answer is simple! Use stronger and longer passwords. Update your router firmware to the latest version and be vigilant while browsing the web. Hide your SSID and make sure your wireless signal range is not that far. Randomly monitor your network and see how many devices are connected to your router or switch.
PMKID WiFi Hacking Attack Download
There is a lot of news spreading on the web that there is something like a ‘PMKID Download‘. To an extent, there are tools that you will need to install that will do the password guessing and exploit the vulnerability for you. Please be cautious when searching online for such tools to hack WPA and WPA-2 wireless networks. The above PMKID attack tutorial is the best method out there that explains the full process to you.
Below are the tools that you will need to download to do a successful PMKID attack:
- Hcxdumptool
- Hcxpcaptool
- Hashcat
Read:
- How to secure your Home WiFi Network Against Hackers?
- How to Remove Malware from your Windows PC (Best Method to Remove Malware)
- How to Know if my PC is Malware Infected? Top Malware Infection Signs (2022)
- Top 4 Ways to Keep Your PC Safe and Clean from Viruses
Update:
As WPA-3 was released there have been vulnerabilities also discovered in it. This allows attackers to perform DoS attacks, Timing attacks and many other hacking methods to gain login credentials.
Decrypting WPA2 using New Kr00k WiFi Vulnerability
Kr00k is a new vulnerability in the popular WPA2 wireless protocol that has just been discovered which directly affects the encryption mechanism of the protocol.
How the Kr00k vulnerability attack works:
The packets WPA2 sends over wireless are encrypted with your WiFi password key. Now, these keys get reset in a rare process called disassociation. Kr00k affects all the latest chips from Broadcom and Cypress.
More specifically, this kr00k is only focused on the following protocols:
- WPA2-Personal
- WPA2-Enterprise
Also, note that these protocols must be using AES-CCMP encryption in order to be exploited so the attacker can get the password.
Mostly affected are Android and Linux devices:
Devices running chips from the companies stated above are all affected until patches are released, various companies including Cisco, Huawei and Apple have already released patches.
How to stay safe from Kr00k?
Watch out for newly released software updates for your network adapters and mobile devices and install them as soon as possible. Also, as a peace of mind, this is not an attack that anyone can do and the attacker has to be close to you and be able to scan to find your network and be in range.
Some precautions you could use:
- Enable MAC-Address filtering
- Keep an eye on your network and who is connected to your wireless
- Check to see if there are any updates available for the router
Conclusion
It’s everyone’s dream about finding out the WiFi password of their friends, neighbors and so on. However, due to the nature of this wireless network technology, there are ways around security and people can actually crack the password. New hacking methods are always released but are patched as soon as they are revealed to the public.
Always be careful about what you click on the internet. Hackers are finding out new methods and ways every day to steal the password of your wireless router. The disadvantage of being hacked is that they can then eavesdrop on your network, intercept traffic and inject harmful malware! Hopefully, after reading this article you will now have learned How to Easily Hack WiFi Network Password using PMKID Attack Method for WPA2 and WPA.






Indeed there are many out there. It would be really awesome if the security teams start to implement this and mitigate the flaw. Hopefully, WPA-3 will fix all of these.
please am getting this error while making the attack
hcxdumptool -o hash -i wlan0mon –filterlist=filter.txt –filtermode=2 –enable_status=3
warning: NetworkManager is running with pid 613
warning: wpa_supplicant is running with pid 669
warning: wlan0mon is probably a monitor interface
reading blacklist line 1 failed: 20:47:DA:3A:EA:21
failed to init globals
You have missed a few steps from the above tutorial, make sure you have downloaded all the tools needed before starting the attack.
Thank you for the tutorial, only thing I would suggest is use Kali Linux for the hacking part.
Great tutorial easy to follow thanks
your tutorial is far more better and clear you explained about the -i monitor and pmkid attack for wifi.
Thank you.
I follow your video but I get this error
–enable_status requires an argument
Should I put 1,2,4,8 ??
4 worked for me but try every digit there and see which one works for you.
Thank you!!