
Wireless network hacking is considered as gathering different information from the computer system and network over the interwork. Today many tools are used to help in network security testing. We have handpicked 6 of the best wireless hacking tools for Windows 10/11 along with free download links.
Contents
6 Best Wireless Network Hacking Tools for Windows 10/11
p0f
This is yet another one on the list, which is deemed to be a versatile and passive operating system fingerprinting tool. It can identify OS on the following
- Machines that can connect to your box (SYN mode),
- Machines that you can connect to (SYN+ACK mode),
- Machines with which you cannot connect to (RST+ mode),
- Machines whose communications you can observe
The best part about this is that it can fingerprint almost anything just by listening, plus it does not make any active connections towards the target machine.
Download p0f 3.0 Latest Version
SuperScan – Great NMAP Alternative
SuperScan is a very powerful TCP port scanner plus a pinger and a resolver. The super scan 4 is yet another update of the viral Windows port scanning tool that is super scan. We suggest you check out this tool if you ever need an alternative for Nmap on windows with a very decent and easy interface.
Yersinia – Harness Vulnerabilities and Test Networks
It is a network tool that is designed primarily to take advantage of some of the weaknesses in different layer two protocols. It is seen as an excellent framework that is used for analyzing as well as testing the deployed systems and networks. Right now following are the network protocols that are being implemented.
Hot Standby Router Protocol (HSRP), IEEE 802.1q, Inter-Switch Link Protocol (ISL), VLAN Trunking Protocol (VTP), Spanning Tree Protocol (STP), Cisco Discovery Protocol (CDP), Dynamic Trunking Protocol (DTP), Dynamic Host Configuration Protocol (DHCP).
SEE ALSO: Download Wireshark Free For Windows 10/11 Latest Version.
John the Ripper – A great password brute forcer
Another one on the list is john the ripper. It is a speedy password cracking tool that is available for many versions of UNIX currently in which 11 are supported officially we are not counting or including the different architectures, win32, DOS, BeOS, and OpenVMS. Its main purpose is to detect UNIX passwords that are very weak.
Besides this, many crypt (3) password hash types that are found mostly on various UNIX flavors, ones that are supported out of the box include Kerberos AFS and Windows NT/ 2000/ 2003/ XP LM hashes along with many more with contributed patches.
NetStumbler
Net stumbler is a very decent tool for windows though it is not as powerful as its Linux counterparts still is our straightforward use and comes with an excellent user interface. It is perfect for the basics of war-driving. It is a tool for Windows that lets you detect WLAN that is a wireless local area network using 802.11b, 802.11a, and 802.11g.
NetStumbler comes with the following uses and benefits:
- It is used to verify that your network is set up the way you intend to.
- It is used to find locations that have inadequate coverage in your WLAN.
- It can detect other networks as well that may be causing interference on your system.
- It is also able to detect unauthorized rogue access points in your workplace.
- It can help you aim for directional antennas for long-haul WLAN links.
- It also used recreationally for War-Driving.
SEE ALSO: Download Cisco Packet Tracer Latest Version 2022 (v7.2.2).
Kismet – Wireless Network Scanner/Sniffer
Kismet is an 802.11 layer two wireless network detector, a sniffer as well as an intrusion detection system. The best part about this tool is that it can work with any wireless card that is supporting raw monitoring mode and can also sniff 802.11b, 802.11a, and 802.11g traffic.
SEE ALSO: Netcat Free Download For Windows 10/11/7 2022.
Some Hacking commands to use with these tools
Ping – Find IP Addresses, Check Hosts, Check Latency
An IP address is used to provide the attacker with the internet address. It is more like a numerical address that goes like 212.214.172.81, which does not reveal too much. You are not able to use ping to convert the address towards a domain name in Windows. It is one of the most popular commands for hacking in Windows 10.
DNS, which is the domain name service protocol, is used to reveal the matching domain name. Ping usually stands for packet internet groper that is being delivered with every system that is compatible with the internet, including all the current versions of windows as well. Please make sure that you are logged on with the net. You need to open DOS and in there enter the following command:
Ping –a securedyou.com
Ping will then be able to search for the domain name and reveal it as well. You shall also be able to get information on the provider that is being used by the attacker like
fibernetsecuredyou.demo.example.com
The first step that is used in hacking the target is pinging. It uses ICMP that stands for internet control messaging protocol that is used to determine whether the target host can be reached or not. Ping is also used to send out the ICMP echo packets towards the target host. If, however, the target host is alive, it shall be able to respond with ICMP echo reply packets.
A ping tool is there with every version of windows. If you wish to ping a remote host, then follow the steps below:
- In the first step, you need to click on the start
- Then click on run
- Now type in ping <ip address or hostname> like ping securedyou.com.
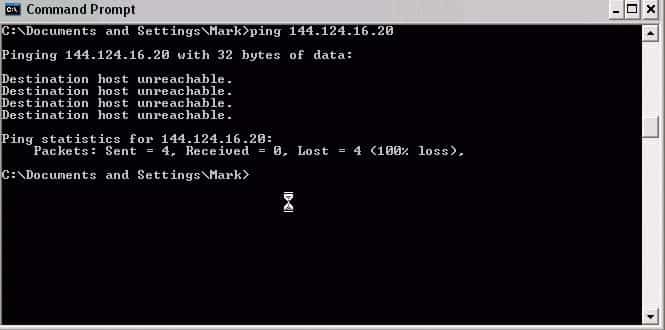
Well, this means that the attacker has logged on by using securedyou.com
Sadly there are many IP addresses out there that cannot be converted into proper domain names.
Ping sweep – Scan for Live Hosts
If somehow you are not determined regarding your target and wish for a live system, then ping sweep is all you need. It also uses ICMP to scan for live systems in a specified range of IP addresses. Although it is similar to ping, it can still reduce all the time that is involved in pinging a wide range of IP addresses. Moreover, Nmap also comes with an option to perform ping sweeps.
Traceroute – Find where and how a request reaches a destination
It is another tool that is used to find out some interesting information about the remote host. Traceroute also uses ICMP. It is also used to help you find out all the information about systems that are involved in sending data from the source towards the destination.
Recommended Tools for Network analysis and scanning:
- Aircrack-ng For Windows 10/11 Download
- Nmap Free Download for Windows 10/11
- Wifite Free Download for Windows 10/11
- Nipper Tools Free Download for Windows 10/11
Final Words: Windows 10/11 WiFi Hacking Tools
So these were the best wireless hacking tools available for Windows 10/11 to download for free. These all have various features, including port scanning, analysis, reporting, and packet capture.







Nice