Are you interested in improving the security of your corporate environment? Adape-Script is an excellent Active Directory Assessment and Privilege Escalation script that you can use to increase the security of your organization’s systems.
Some features include:
- NBT-NS spoofing and LLMNR.
- It shall be able to check for the GPP passwords.
- Gather hashed for a various account through Kerberos
- Map out the domain
- Identify targets through BloodHound.
- It shall be able to check out for the privilege escalation methods.
- Also able to search for the open shares on the network.
- It can search for the shares as well as other accessible directories for sensitive strings and files like passwords or whatever you wish for. It indeed looks for the term password by default.
- Able to search for the patches of systems on the network.
- Search for the file servers
- Able to search for the attached shares
- Able to gather the domain policy.
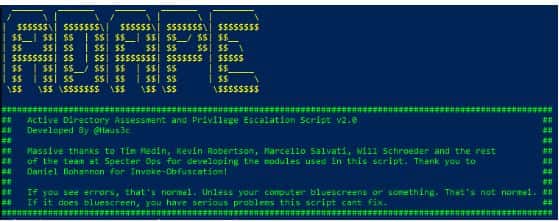
The script is going to run on its own entirely without using any internet connection. The scripts required are obfuscated power shell and included, so it shall bypass most basic AV solutions. It shall turn off the Windows Defender by default. If, in any case, OpSec is worrying you, then you can comment it out by putting a “#” before “Set-MpPreference- DisableRealtimeMontioring $true” on line 21.
SEE ALSO: Download OpenVAS Free Vulnerability Scanner (Latest).
Contents
ADAPE Script Modules:
- Inveigh
- Kerberos
- Bloodhound
- Get-GPPP
- PowerUp
- PowerView
As required, the script shall ask to run as admin, if you do not have the admin access then it shall only run the privilege escalation module. We recommend that you run the following bypass UAC script if you are being blocked by it.:
Once you have run the .pst1; it shall create for you the capture file in the same folder it’s running in and zips it as well. All the folders except .zip files are deleted at the end of the script.
GPP password checking as well as searching for the sensitive files will take some time; therefore, you do not need to be surprised at all if it is takes more time to finish as it depends upon the number of domain controllers, string you are searching for and the open shares.
SEE ALSO: Download BeEF Browser Exploitation Framework For Free.
Why Active Directory Assessment and Privilege Escalation is important

This takes place whenever a malicious user exploits a bug, configuration error, or a design flaw there in any application or OS to gain elevated access towards resources that, in reality, should be unavailable to that particular user.
The attacker is then able to use the privileges that he has just gained to steal all the confidential yet private data, then run the administrative commands or deploy the malware and, in the end, cause some severe damage to users’ OS, organization, server apps as well as its reputation. With the help of these, users can protect all the accounts in their systems and apps to maintain a perfect security posture.
SEE ALSO: Download Wapiti Web Application Vulnerability Scanner.
How to use ADAPE-Script for Privilege Escalation

Now in this, the attackers begin by exploiting privilege escalation vulnerability in a target app or system; this lets them override the limitations of the current account of the user. Then like this, they get access to the function and data of another user (horizontal privilege escalation) or obtain the elevated privileges probably of a system administrator or any other power user (vertical privilege escalation). Such things are usually undertaken in preparation for the main attack.
The miscreants remain there on the same general user privilege level. Still, they can access data as well as the function of the other accounts or processes that needs to be unavailable to the current processor account in horizontal privilege escalation.
For example, this might mean using a compromised office work station to gain access to the other office user’s data. Now for the web apps, one of the examples of this may be getting access to the profile of another user or platform for e-commerce or their bank account on an e-banking site.
Vertical privilege escalation is potentially more dangerous. It is also known as privilege elevation. In this, the attackers begin with a fewer privileges account to obtain the rights of a more compelling user, most probably the administrator or the system user on Microsoft Windows, or root on Unix and Linux system.
Now with the elevated privileges, the attacker can wreck all kinds of Havoc in the computer system and apps: steal the access credentials and other private yet sensitive information, download and then execute the malware, erase data or execute the arbitrary code.
Worse than this is the skilled attackers can use the elevated privileges of their activities. This usually leaves the victim not aware that an attack has taken place at all. Like this, the cybercriminals can steal information or plant malware in the company system directly.
SEE ALSO: Download IBM Security App Scan for Free.
Other Hacking Tools you will love to play around with:
- Download Commando VM Hacking OS.
- A collection of the 15 best Hacking tools and utilities of 2020.
- Download wwwhack v1.9 Free.
ADAPE-Script Download – Active Directory Assessment and Privilege Escalation
AD is integrated so much in enterprise environments that making it secure is a necessity. Adape Script provides you a tremendous upper hand if you want to do privilege escalation in your Active Directory environment.







Can you hack Active Directory permissions with this?
Indirectly yes, it is used for escalating privileges in an AD environment so you can do administrative tasks without permission from group policies etc.