
OSINT is a Cybersecurity framework meant for gathering information. It is a collection of OSINT tools 2022 that are used to make your Intel and data collection tasks easier. The security researchers and penetrations testers use this one for the following purposes:
- Digital footprinting
- OSINT research
- Intelligence gathering
- Reconnaissance
The tool comes with a simple web-based interface that allows the users to browse different tools that to are filtered in terms of categories. Moreover, it also provides a functional classification of all the Intel sources that exist for the public what infosec areas the users are neglecting to explore or what are going to be the next steps for the investigation.
On various topics and goals, this framework is classified, which can be seen while having a look at the OSINT tree available via the web interface.
Contents
Classification of OSINT Framework
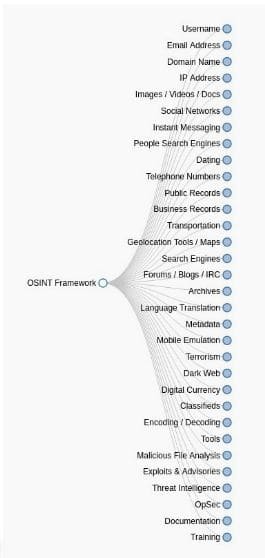
You need to visit the website https://www.osintframework.com. Once there, you shall see the tree on the left side of the screen.
There are a few highlights that the users need to know, take a look at the following indicators on the right side for the listed tools:
- (T) – This is used to indicate a link to a tool that needs to be installed and then run locally
- (D) – Google Dorks also known as Google Hacking Database.
- (R) – It requires registration.
- (M) – This is used to indicate a URL that carries the search term, and the URL itself needs to be edited manually
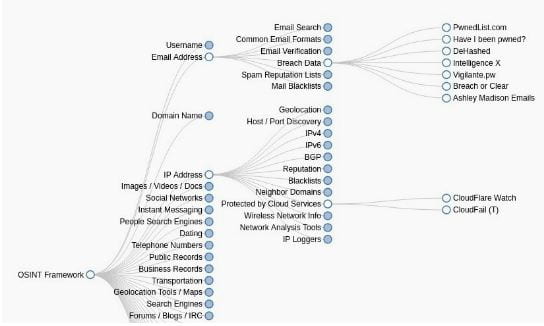
Now when the user clicks on any category like username, email address, or the domain name, then various useful resources appear on the screen in the form of a sub-tree.
If you have all the tools present in a single interface, then searching for users, email address, IP addresses, and social network details become easier. It is the same as a vast OSINT bookmarks library.
E.g., There within the IP address, specifically via the protected by the cloud services section, users shall be able to find links to CloudFail and Cloudflare Watch.
The same happens with the email address that is another popular category. Breach data, and you shall be able to find many beneficial resources like Dehashed or Have I been Pwned?
The framework can provide various ways to scan ports. These are as followed:
- ZoomEye
- Looquer
- io
- Shodan
Social network data exploration can be made available by providing access to different tools like Reddit, LinkedIn, Google+, Facebook, and Twitter.
SEE ALSO: Cyphon – Open Source Incident Alert Tool Download.
LinkedIn is not as exploited as a network if compared with Twitter or Facebook. The framework provides with best tools such as ScrapedIn, LinkedIn, and the IntelTechniques LinkedIn tool.
If we talk about the domain and DNS history, then users shall be able to find tools there in the section of PassiveDNS, including our own SecurityTrails toolkit, Mnemonic, DNS Dumpster, and PTRarchive.com.
Now keep in mind that with the SecurityTrails, users can take a quick look there into the domain DNS history and with this useful information regarding the IP addresses, records of Historical IPs, history of WHOIS as well as correlate all that certain information in a single place.
Tools bundled with OSINT
It comes with yet another exciting category that is “vulnerabilities.” This can be found within the Domain Names category that is used to provide access to many good as well as top CVE databases. These are as followed:
- org
- Zone-H.org
- ASafaWeb
- Sn1per
- Mage Scan
Do you wish to identify the phone numbers? Today various tracking tools can be used to identify an incoming call. These are as followed:
- Free Carrier Lookup
- Phone Validator
- ThatsThem
- CallerID Test
- Who called
- OpenCNAM
- HLR Lookup Portal
- Data24-7
- Next Caller
- Number
Users are also able to find a category that is dedicated to the Dark web; classified into five subsections which are as followed:
- General information
- Dark web clients
- Content discovery
- TOR search
- Directories
SEE ALSO: ADAPE-Script for Active Directory Permissions Hacking.
A variety of search engines to gather information
Now it only takes a few seconds to access the dark web tools and the popular websites by using .onion with the following features:
- Onioff
- Tor Scan
- OnionScan
- Ahmia
- OnionLinkDeepDotWeb
- I2P Anonymous Network (T)
- Tor Download (T)
- Onion Investigator
- docker-onion-Nmap (T), an alternative to the original Nmap tool.
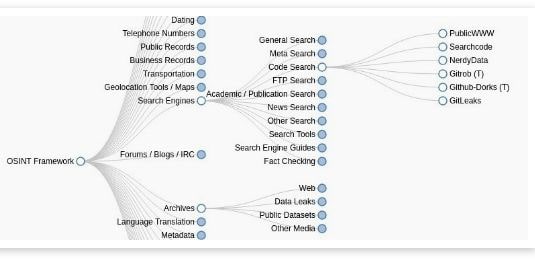
Code search is yet another useful category that gives access to websites that are specialized in code search.
All the sites can be used to search for lines of codes on the past as well as present projects, companies, online repositories, and many others. Following are some of the best:
- Gitrob (T)
- Github-Dorks (T)
- NerdyData
- PublicWWW
Another great section by the name “Archives” also exit. This features links to popular websites as well as tools for getting back the historical information. It carries the following popular options:
- Wayback Machine – Beta Search
- com
- UK Web Archive
- com
- Cached Pages
- Cached View
- WebCite
- isWaybackpack
- Browsershots
- Bounce
- PDFmyURL
- Wayback Machine Chrome Extension
- Common Crawl
SEE ALSO: The 6 Best Free SQL Injection Tools of 2022 (Download).
In the very same category lies another section by the name “Data Leaks.” This one provides quite interesting leaks from critical extracted data that is removed and then published on popular sites like Cryptome and WikiLeaks.
Now on the lowest part of the framework resource tree, you shall be able to find other tools that are used to provide help to your investigation when no individuals are involved like OpSec, code analysis, malware identification, metadata analysis, and much more. It carries the following popular tools:
- Joe File Analyzer
- Ether
- MalwareViz
- Hybrid Analysis
- Malwr
- VirusTotal
- ExifTool
- FOCA
- Metagoofil
- Sandbox
- ee Cuckoo Sandbox
Now browsing the OSINT framework website, then there are various ways in which you can get data regarding any target that you are investigating.
Moreover, it can be used as a useful Cybersecurity checklist to see what areas are left to explore while you are analyzing an individual or any company out there.
SEE ALSO: The Best Search Engines for Privacy Power Users.
OSINT-Framework (OSINT Tools) Download – Cybersecurity Intel Gathering Tool
Information gathering and Intel is one of the most vital steps when you are doing security research. This is where the OSINT framework and OSINT Tools 2022 come in handy. I hope you have enjoyed this new article and will use all the goodies it has to offer. We have also provided a PDF version of the documentation should you wish to need it.






