Humans tend to keep security a very integral part of our daily lives. However, the only part we particularly miss out on keep the digital life secure and safe! This is why today we are sharing with you how to remove virus with CMD in Windows 10 and Windows 11. We will also be showing you how to remove shortcut virus and use popular methods like attrib.
Different types behave differently. Know them all! Now to start with what is it? It is a simple program that makes your system act in an undesirable way. It is designed to:
- Drag your system down.
- Erase all critical files.
- Track habits.
- Give an entry point to hackers to personal information.
Popular ones known as Locky and CryptoLocker are known as ransomware:
- Can delete the system files.
- Encrypt them.
- Change the file extension to .locky or .encrypt.
- Hide all files and leave users with nowhere to unhide them.
Once you find it in your system, you would want to remove it. Mostly CMD.exe is used to remove them.
Contents
Why Virus Removal with CMD is a wise choice
Using the command line does not check or remove from your system or any external storage device.
- Removes the virus by showing hidden infections on a drive or partition, and after that, the suspicious file can be deleted.
By their nature viruses always conceal themselves. A question may arise that how you can show the hidden files using CMD? You need the attrib command which is a command prompt used to:
- Display, set or remove attributes of files or folders from the selected location.
As you cancel the hidden attributes, it shall appear in the folder, and you would know where to find it, and then it can be removed.
5 Ways on How to Remove Virus from PC using Command Prompt
Using attrib command
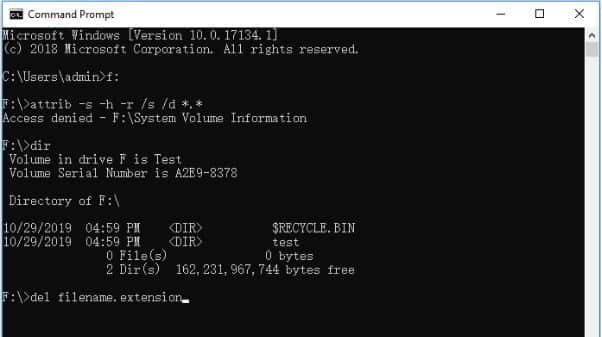
For this:
- In the search box type cmd. Click right on the command prompt and select Run as administrator.
- Type F and hit enter. (F can be replaced with the infected device or partition).
- Type in attrib –s –h –r/s/d *.* and press enter.
- Then type in dir and press enter. You would be able to see files under the particular drive as this command is used to display a list of a directory’s files as well as subdirectories.
Necessary attributes of attrib command
- R is the Read-only attribute of any file or folder. It means the file cannot be written or executed.
- H is Hidden attribute.
- A is Archiving used to prepare the file for it.
- S is a System attribute, used to change the selected files or folders from user files into system files.
- I am the not content indexed file attribute.
The “attrib” Syntax:
ATTRIB [+ attribute | – attribute] [pathname] [/S [/D]]
- + / –: Used to enact or to cancel the specified attribute.
- Attribute: As explained above.
- /S: used to Search throughout the entire path, including subfolders.
- /D: It includes any process folder.
- Pathname: Where is the malicious content located.
SEE ALSO: Best Methods to Identify if you are infected with a Malware or Rootkit.
Command Syntax:
ATTRIB [+R | -R] [+A | -A ] [+S | -S] [+H | -H] [+I | -I] [drive:][path][filename] [/S [/D] [/L]]
Note: keep in mind that improper use of cmd can result in system damager; therefore, be careful in using the command prompt.
Now if you receive any message saying access denied then:
- Be sure that you run it as an administrator.
- Be sure the folder or file is not in any use.
- You will need to make sure to review the account permissions and to have control over the file or folder. For this right-click on the file/folder/partition and click on security.
- Use the command CHKDSK to check for any system errors. For this run cmd.exe and enter chkdsk /f [Insert drive letter].
For computer professionals, manual input of the command line is recommended as the wrong commands can cause problems. We recommend that for security and un-stability you go with an automatic command line alternative.
- Check and fix files system errors.
- Enable or disable write protection and system update with a single click inspite of typing in an intricate command line.
Follow the steps to show hidden files:
- Then start it. Choose file showing there on the left pane and then click on the target drive for scanning.
- As the operation completes, you need to click on the view button to check for hidden files.
SEE ALSO: 4 Field-Tested Methods on Keep your Windows 10/11 Installation Virus-Free.
Windows Defender as a Backup Plan – Removes Hidden Viruses

This is in-built protection in Windows 10. It is used to:
- Provide protection and security against all sorts of threats, malware, and spyware for your system and the connected devices.
If you somehow do not have third-party apps, then we recommend you use a built-in utility. For this:
- Go to settings > update and security > windows security.
- Then click on virus and threat protection.
- In its history section, select scan now to scab for all the occurrences on the system.
SEE ALSO: The Best Ways on How You Can Remove Arcade Spot Games Redirect Virus.
Run an Internet Security Suite Scan
Every system out there today has antivirus software installed. Now when you find out your system is infected, you need to:
- Perform a full system scan of all drives.
- Remove or add to the quarantine list any infected files you may find.
My personal picks:
Nuke the drive
Now, what is formatting? It is a process that is used to erase existing files that are selected on a particular drive or partition. This shall remove the virus for sure. Be sure that you do not have any important files stored on the device as this process will cause data loss.
SEE ALSO: How to Create a Bootable USB Drive using CMD in Windows 10/11.
Future tips to reduce infections

You should keep in mind all the ways on how to prevent infection on your system or any external storage device.
Adopt the following tips:
- Make sure that you have a safe and secured network connection.
- You need to be cautious with the origins of the programs that you wish to install.
- Avoid all suspicious sites and think twice before making a click.
- Keep a backup of all the files with the help of free backup software to avoid complete loss of data that may be caused by an infection.
SEE ALSO: How to Create a Harmless Virus using Notepad Scripts.
Are you scanning for viruses with CMD?
Is there a method not shared above that you are using to remove viruses with CMD? Do let us know below in the comments and we will add them above. My favorite method involves using “attrib”. The most annoying removals which I have done include the shortcut and hidden files.